Medusa Ransomware: How It Works, Who It Targets, And How To Stop It
10 April 2026
8 Mins Read
- What Is Medusa Ransomware?
- What Really Makes Medusa Threatening?
- How Medusa Communicates With The Outer World?
- Medusa vs. MedusaLocker: Know The Difference
- How A Medusa Ransomware Attack Unfolds?
- Stage 1: Initial Access
- Stage 2: Lateral Movement And Privilege Escalation
- Stage 3: Data Exfiltration
- Stage 4: Encryption And Double Extortion
- Why Are Medusa Ransomware Gang Phishing Campaigns So Hard To Catch?
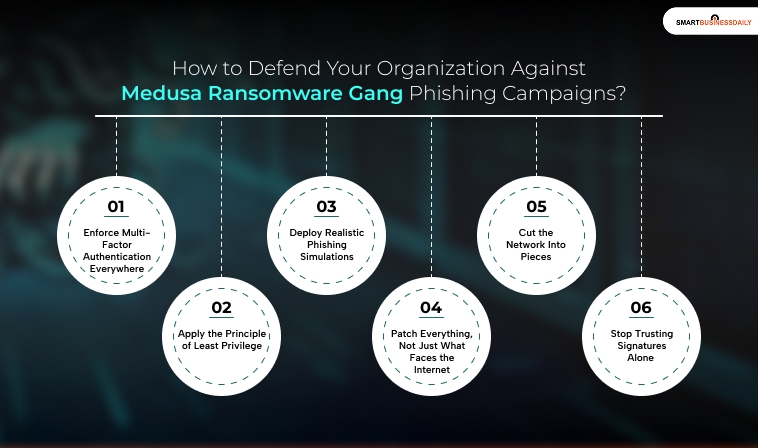
- How To Defend Your Organization Against Medusa Ransomware Gang Phishing Campaigns?
- 1. Enforce Multi-Factor Authentication Everywhere
- 2. Apply The Principle Of Least Privilege
- 3. Deploy Realistic Phishing Simulations
- 4. Patch Everything, Not Just What Faces The Internet
- 5. Cut The Network Into Pieces
- 6. Stop Trusting Signatures Alone
- What Can You Do To Stop The Attacks In 2026?
Are you running your own business?
If you answered yes, I’m sure you are aware of the Medusa ransomware threat. The medusa ransomware gang phishing campaigns are the biggest threats that growing businesses face today.
This cyber threat surfaced in 2022. After that, it has attacked companies across most sectors. Especially those in healthcare, education, and finance. But in 2024, the Medusa ransomware gang phishing campaigns started rolling out fast, as the FBI says.
Wait, are you still treating it as just another paltry cyber threat? It’s a mistake that can cost you time, money, and trust. So, act before it affects your business, too.
What Is Medusa Ransomware?
Medusa is not just malware. It’s a cybercrime group. The group operates on a ransomware-as-a-service model. In other words, it recruits external operators to carry out attacks. Meanwhile, the core team maintains the infrastructure and takes a cut.
It surfaced in late 2022. But, within a year, it had broken into the top ten most active ransomware groups on the planet. Most importantly, Toyota Financial Services got hit. So did the Minneapolis Public School District.
Simply put, Medusa mainly targets industries where downtime hurts the most. That includes hospitals, schools, banks, and critical infrastructure. When systems go down, pressure rises. In the meantime, Medusa uses that pressure to force fast payouts.
Most security teams believe the group operates from Russia or a closely aligned region. To clarify, Medusa is active on Russian-language crime forums. Above all, it uses slang common in those circles.
At the same time, it also avoids attacking companies in Russia and CIS countries. For them, money is the main goal. However, its targeting choices also suggest political alignment.
What Really Makes Medusa Threatening?
Medusa runs its operations publicly. Their confidence shows that they are always one step ahead. That’s what makes them more dangerous.
Most importantly, their innovative threat landscapes pose a major challenge for small companies. They can somehow protect their business from consumer fraud. But these threat landscapes are severe!
How Medusa Communicates With The Outer World?
Its data-leak site, known as Medusa Blog, operates on the dark web. But the group doesn’t stop there. It also runs its own Telegram channel, has a Facebook profile, along with a proper X (formerly Twitter) account under the name “OSINT Without Borders.”
These public platforms increase pressure on victims. Simply put, this strategy helps Medusa build both fear and credibility.
Medusa vs. MedusaLocker: Know The Difference
This is one of the most important distinctions in cybersecurity today. Yet many articles still miss it.
MedusaLocker is a separate ransomware strain. It first appeared in 2019. Most attacks spread through exposed RDP ports or basic phishing emails. In simple terms, it is loud, noticeable, and often detected early. It does not have the same level of control or accuracy as the Medusa ransomware group.
At the same time, there are two other threats with the same name. This is where confusion starts.
One is a mobile banking trojan. It runs on a malware‑as‑a‑service model. It targets Android phones and steals financial data.
The other is a botnet. It first showed up on darknet forums in 2015. Later, it was rebuilt using leaked Mirai code. Its main goal is to launch DDoS attacks and knock systems offline.
These three threats do not share code. They do not use the same servers. The same people do not run them.
This mix‑up causes real problems. If you follow the wrong indicators of compromise, you waste time. You keep chasing signatures that do not matter. Meanwhile, the real threat stays active.
A rule built to detect the botnet will not stop the ransomware group. A detector made for the mobile Trojan will not catch Medusa’s phishing emails. Each threat behaves differently.
That is why understanding Medusa ransomware phishing campaigns is critical. Without that clarity, even strong security tools can miss the real attack.
How A Medusa Ransomware Attack Unfolds?
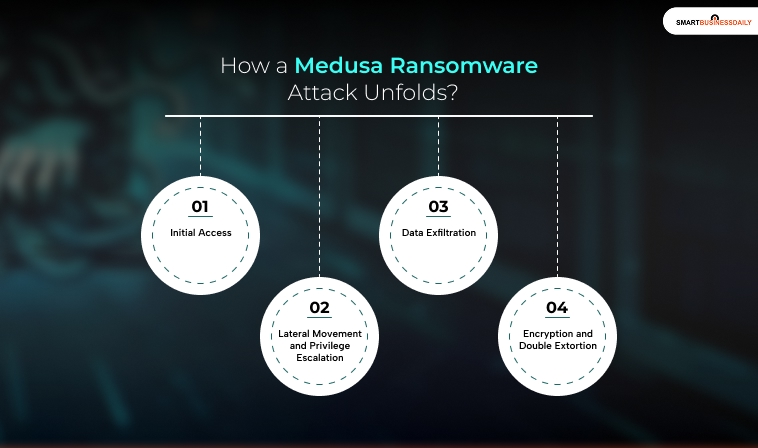
Medusa attacks follow a deliberate, multi-stage process. Here is each stage explained clearly:
Stage 1: Initial Access
Medusa breaks into networks in just a few ways. The first is phishing. Medusa can run its own phishing campaigns when needed. But most of the time, it does not start from scratch. It buys access instead.
This is where Initial Access Brokers come in. These brokers break into company networks using stolen passwords, brute‑force attacks, or phishing. They do not care what happens next. Their only goal is to get inside.
Once they succeed, they sell that access on criminal forums. Medusa often appears as the buyer. The group openly asks for “good network access” to companies in the US, Canada, Australia, the UK, Italy, and Germany.
Medusa ransomware phishing campaigns are not random. Before sending a single email, the attackers do research. LinkedIn is their main tool. They study staff roles, team structures, and vendors.
When the email arrives, it looks familiar. It matches your company’s real email style. In many cases, it pretends to come from a vendor you already work with.
Timing also matters. Medusa sends attacks during busy periods. Month‑end close is a common choice. That is when teams rush to approve invoices. People ask fewer questions. Small mistakes slip through.
This mix of planning, timing, and trust is what makes these campaigns effective.
Stage 2: Lateral Movement And Privilege Escalation
Once inside, nothing dramatic happens immediately. Meanwhile, Medusa uses PowerShell and other built-in Windows tools to quietly poke around. Firstly, it maps the network, extracts credentials using OS-dumping techniques, and tests how far those credentials actually extend.
They don’t hack a compromised account that can only access one system. However, they are more interested in an account with broad permissions. That gap is exactly what Medusa looks for.
Stage 3: Data Exfiltration
Before any encryption takes place, Medusa steals sensitive data. It launches its ransomware binary, gaze.exe. This ransomware sets up the environment for exfiltration. After that, PowerShell scripts transfer the data over TOR-protected channels. In the next step, the stolen data is posted to the Medusa Blog. This is the group’s dark web leak site, with a countdown timer, victim information, and a ransom demand.
Stage 4: Encryption And Double Extortion
Medusa then encrypts all accessible files, appending the “.MEDUSA” extension. However, you will also get a ransom note titled !!!READ_ME_MEDUSA!!!.txt
This note is dropped in every folder containing encrypted files. Above all, the note contains payment instructions and a unique victim identifier. But why do they use this double extortion model?
It means that even with backups, you still face a public data leak if you refuse to pay. However, at that time, victims must decide whether paying is worth it. In the same vein, you must know that doing so funds further attacks. At the same time, it provides no guarantee that the data will remain private.
Also Check: How Is Technology Ftasiamanagemnet Boosting Your Business’ Growth And Security In 2025 And Beyond?
Why Are Medusa Ransomware Gang Phishing Campaigns So Hard To Catch?
The main reason Medusa ransomware gang phishing campaigns are hard to catch is timing.
The emails arrive when teams are under pressure. During payroll week. At quarter‑end. Or right after a vendor contract is signed. At those moments, people are busy and distracted. They move fast. They click links without stopping to think.
Attackers take advantage of that rush. Fewer checks happen. Small red flags are missed. When you are building a business from scratch, such mistakes can easily occur.
Medusa also hides behind trusted senders. Many phishing emails come from accounts already compromised inside the company. So the message does not come from a stranger. It looks like it came from a coworker.
That detail matters. When an email appears to come from someone on your team, your guard drops. You trust it. You do not pause to verify. And that hesitation is exactly what Medusa counts on.
How To Defend Your Organization Against Medusa Ransomware Gang Phishing Campaigns?
The following steps address Medusa’s actual attack chain. Before we start, remember that you cannot do that with general security hygiene alone.
1. Enforce Multi-Factor Authentication Everywhere
MFA is your most effective barrier against credential-based access. Even if Medusa or an IAB obtains valid login credentials, MFA blocks unauthorized entry without the second factor. Apply it to every account, every remote access tool, and every admin panel.
2. Apply The Principle Of Least Privilege
Limit each account’s access to only what is needed for that role. No single account should have access to both customer data and administrative controls. This limits how far an attacker can move once they gain initial access. Use role-based access controls and regularly audit permissions.
3. Deploy Realistic Phishing Simulations
Generic phishing training is not enough. Run simulations that reflect how Medusa actually operates. For example, you can include role-specific lures, trusted-sender spoofing, and context-aware timing. Above all, the staff should learn to pause and verify even when an email looks completely legitimate.
4. Patch Everything, Not Just What Faces The Internet
Getting in is only step one for Medusa. After that, it starts scanning for anything unpatched that it can move through.
In the same vein, the mistake most teams make is patching only what faces the internet, leaving internal machines to drift. Behind the firewall does not mean safe once an attacker is already sitting on the network.
So, operating systems, firmware, and applications need to stay up to date. In the same vein, Windows 10 deserves special mention. If Windows 10 is still on your network, you must know that its support ended in October 2025.
5. Cut The Network Into Pieces
Flat networks are a gift to attackers. If Medusa compromises one machine and can reach everything else from there, it means your segmentation has failed. Therefore, break the network into zones.
In addition, keep sensitive data and critical systems walled off from general access. Remember, the goal is to make lateral movement slow, noisy, and expensive.
6. Stop Trusting Signatures Alone
Medusa’s phishing lures are custom-built. Its credential dumping uses legitimate Windows functions. But simple signature-based tools can’t detect any of those. In the SS,e vein, email security needs SPF, DMARC, and DKIM enforcement at a minimum.
On endpoints, you have to install a behavior-based detection. For example, check any account downloading gigabytes of files at 2 am.
What Can You Do To Stop The Attacks In 2026?
Medusa ransomware gang phishing campaigns are not slowing down. The group buys access, waits, steals data, and then encrypts. However, paying the ransom does not guarantee anything.
But most of the weak points in Medusa’s chain are fixable without a massive budget. For instance, MFA stops credential abuse. If you leave the least privilege, it limits your blast radius.
In addition, segmentation slows Medusa’s movement. I also suggest immutable backups to remove any encryption leverage. Most importantly, you must offer realistic training to your team. The group runs its operation like a business. Treat your defenses the same way.



















Comments Are Closed For This Article